AI-Generated Content — Research-backed, not based on personal experience
This post contains affiliate links. We may earn a commission at no extra cost to you.
10 Best Zero Trust Security Platforms for Enterprise: Complete Buyer's Guide
Expert analysis of the top zero trust security platforms for 2026, comparing features, pricing, and deployment strategies for enterprise security teams.
Enterprise security audits reveal a sobering reality: the majority of data breaches involve human error or compromised credentials, according to industry research. Traditional perimeter-based security models are failing spectacularly in an era where the corporate perimeter has dissolved into remote work, cloud migrations, and hybrid infrastructure.
Zero trust isn't just another security buzzword anymore.
It's become the default architecture for organizations that understand the fundamental shift happening in enterprise security. Let me tell you, the "trust but verify" mentality died somewhere around 2020, and what replaced it is far more sophisticated.
The zero trust market has matured significantly since its early days. We're no longer talking about single-point solutions or pilot programs. Enterprises are increasingly implementing full zero trust architectures that span identity verification, device compliance, network microsegmentation, and data protection. And this matters because the stakes have never been higher.
But here's where it gets complicated. The vendor won't tell you this but choosing a zero trust platform isn't just about picking the shiniest dashboard or the most features. It's about understanding your organization's risk profile, existing infrastructure, and long-term security strategy. Some platforms excel at network access control but fall short on identity management. Others provide strong device compliance but struggle with legacy system integration.
In practice, the most effective zero trust implementations combine multiple specialized platforms rather than relying on a single vendor's all-encompassing solution. This guide cuts through the marketing noise to examine what actually matters when evaluating zero trust platforms for enterprise deployment.
What Makes a Zero Trust Platform Enterprise-Ready
Identity Verification and Access Control
Zero trust starts with identity, and enterprise-grade platforms need to go far beyond simple username and password verification. The most effective solutions implement continuous authentication that evaluates user behavior, device health, contextual factors, and session patterns throughout each interaction.
Platforms with adaptive authentication policies can significantly reduce false positives compared to static rule-based systems. This means fewer help desk tickets and less user friction while maintaining security posture.
Look for platforms that can integrate with your existing identity providers (Active Directory, Azure AD, LDAP) while adding behavioral analytics and risk scoring on top.
Device compliance checking has become equally critical. Compromised endpoints represent a significant attack vector in many successful breaches. Effective zero trust platforms continuously monitor device health, patch levels, and security configurations before granting access to resources.
Network Microsegmentation and Policy Enforcement
Traditional network security relied on castle-and-moat thinking: hard perimeter, soft interior. Zero trust flips this entirely.
Every network segment, every application, every data repository requires explicit access policies based on user identity, device state, and business context.
Enterprise security frameworks demand granular policy controls that can be applied consistently across on-premises, cloud, and hybrid environments. Actually, let me be more specific about that. The vendor won't tell you this but many platforms struggle with policy consistency when spanning multiple environments. Look for solutions that provide centralized policy management with distributed enforcement points.
In practice, the most successful deployments implement microsegmentation gradually, starting with high-value assets and expanding coverage over time. Platforms that support phased rollouts with detailed visibility into traffic flows make this process manageable rather than disruptive.
Integration Capabilities and API Access
Enterprise environments are complex networks of security tools, business applications, and infrastructure components. Zero trust platforms that operate in isolation quickly become security theater rather than effective protection.
Organizations using platforms with strong API integrations typically achieve faster time-to-value compared to those requiring extensive custom integration work. Your zero trust platform should integrate smoothly with existing SIEM solutions, endpoint protection platforms, and identity management systems.
Cloud-native platforms typically offer better integration capabilities than legacy solutions retrofitted for zero trust. However, organizations with significant on-premises infrastructure need platforms that can bridge hybrid environments effectively.
Top Zero Trust Security Platforms for Enterprise
Best for Full Enterprise Deployment: Palo Alto Networks Zero Trust

Palo Alto Networks has built their zero trust platform around the concept of "never trust, always verify," but with the enterprise-grade infrastructure that large organizations actually need. Their approach combines ZTNA (Zero Trust Network Access) with broader security service edge capabilities, creating a platform that works whether you're securing remote workers or protecting on-premises data centers.
The platform's strength lies in its integration with existing Palo Alto security infrastructure. Organizations already invested in Palo Alto firewalls and network security can extend their investment rather than replacing it entirely.
Enterprises with existing Palo Alto infrastructure can reduce implementation time when adopting their zero trust platform.
However, this integration advantage becomes a limitation if you're not already in the Palo Alto world (and many organizations aren't). The platform works best as part of a broader Palo Alto security strategy, which can mean vendor lock-in and higher long-term costs. Some organizations report that the learning curve for administrators unfamiliar with Palo Alto's management interfaces can be steep.
Check out Palo Alto Networks Zero Trust → offers enterprise-grade scalability and proven deployment models for large organizations.
Best for Cloud-Native Organizations: Zscaler
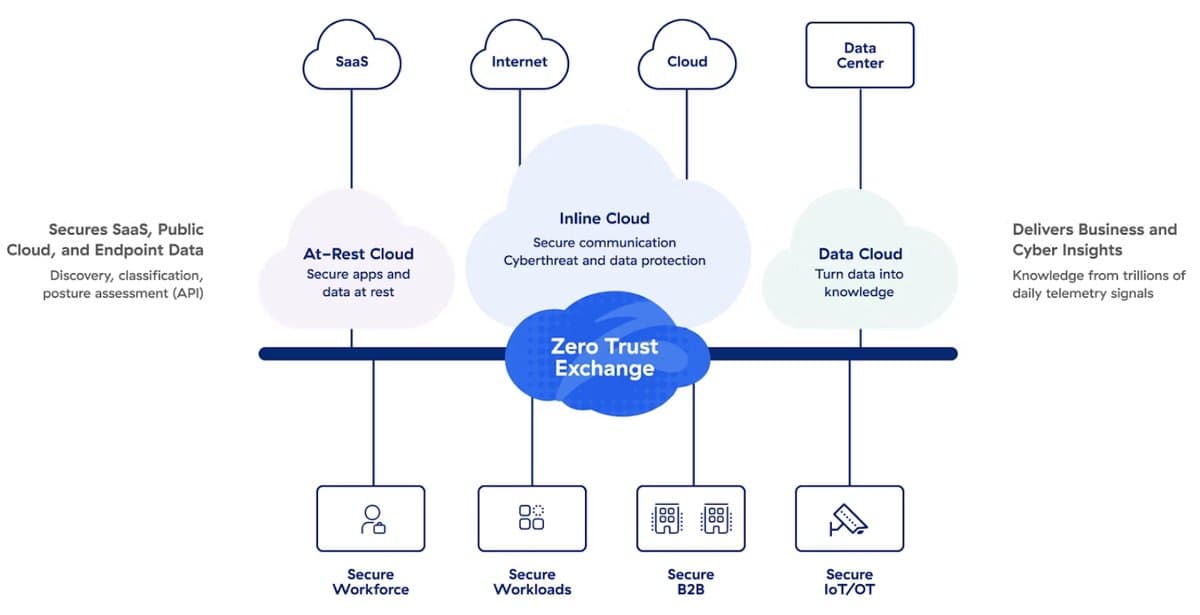
Zscaler built their platform from the ground up as a cloud-native solution, and it shows in every aspect of their zero trust implementation. Rather than retrofitting traditional network security concepts, they reimagined how zero trust should work in a cloud-first world.
The platform acts as a secure gateway between users and applications, regardless of where those applications live. This approach eliminates the complexity of VPN management while providing granular access controls based on user identity, device posture, and application requirements. Organizations using Zscaler's approach can significantly reduce their attack surface compared to traditional VPN-based remote access solutions.
Zscaler's cloud-native architecture provides natural scalability and global presence that traditional platforms struggle to match. Remote workers get consistent performance regardless of location, and IT teams manage policies from a centralized console that spans the entire organization.
The trade-off is dependency on Zscaler's cloud infrastructure. Organizations with strict data sovereignty requirements or concerns about cloud dependency may find this approach limiting. And here's something else: the platform's cloud-first design can create challenges when integrating with legacy on-premises systems that weren't designed for internet-first connectivity.
Best for Microsoft-Centric Environments: Microsoft Entra

Microsoft has transformed their identity platform into a zero trust solution that extends far beyond traditional Active Directory capabilities. Entra (formerly Azure AD) now includes conditional access policies, device compliance checking, and application protection that creates a zero trust framework particularly well-suited for organizations already invested in Microsoft's world.
The platform's integration with Office 365, Azure, and Windows creates a smooth zero trust experience for users while providing administrators with detailed visibility into access patterns and risk factors. Organizations report that users barely notice the additional security controls, which is critical for maintaining productivity during zero trust implementation.
Microsoft's pricing model makes Entra particularly attractive for organizations already licensing Microsoft enterprise services. The zero trust capabilities come bundled with higher-tier Microsoft licenses, creating economic advantages that standalone platforms can't match.
But here's the limitation: Entra works best when your entire technology stack is Microsoft-centric. Organizations with diverse application portfolios or significant non-Microsoft infrastructure may find gaps in coverage that require additional security tools. The vendor won't tell you this but some advanced zero trust features are only available at the highest license tiers, which can drive up costs significantly.
Check out Microsoft Entra → provides integrated identity and access management with zero trust controls built for Microsoft environments.
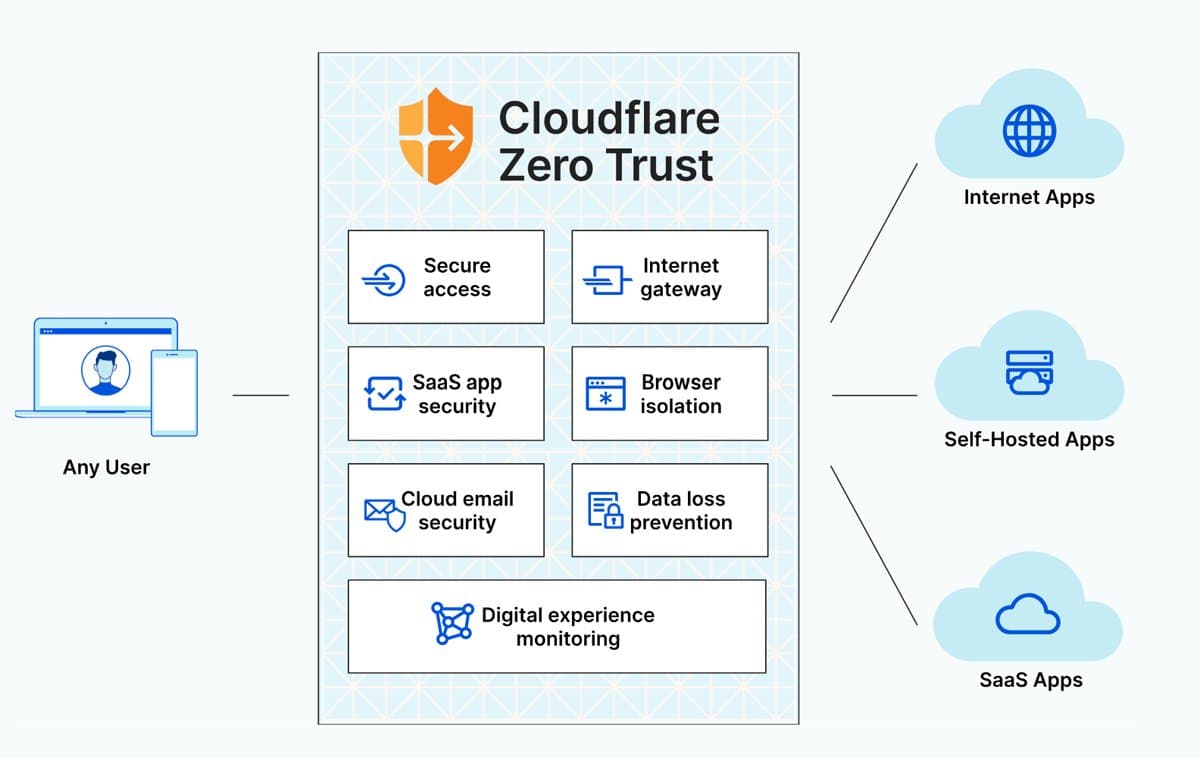
Best for Fast ZTNA Deployment: Cloudflare Access

Cloudflare Access takes a different approach to zero trust, focusing specifically on network access control rather than trying to be a complete security platform. This targeted approach makes it particularly effective for organizations that need to secure access to self-hosted applications and legacy systems without deploying traditional VPNs.
The platform uses Cloudflare's global network infrastructure to provide fast, secure access to applications regardless of user location. Rather than routing traffic through centralized VPN concentrators, Cloudflare Access uses distributed enforcement points that reduce latency while maintaining security controls.
Organizations can typically implement Cloudflare Access for specific applications quickly, making it ideal for rapid zero trust pilots or emergency remote access needs. The platform's simplicity is both a strength and a limitation. It excels at its core mission but doesn't provide the full zero trust capabilities that large enterprises typically need.
Check out Cloudflare Access → offers fast deployment and global performance for zero trust network access requirements.
Best for Identity-Centric Zero Trust: Okta
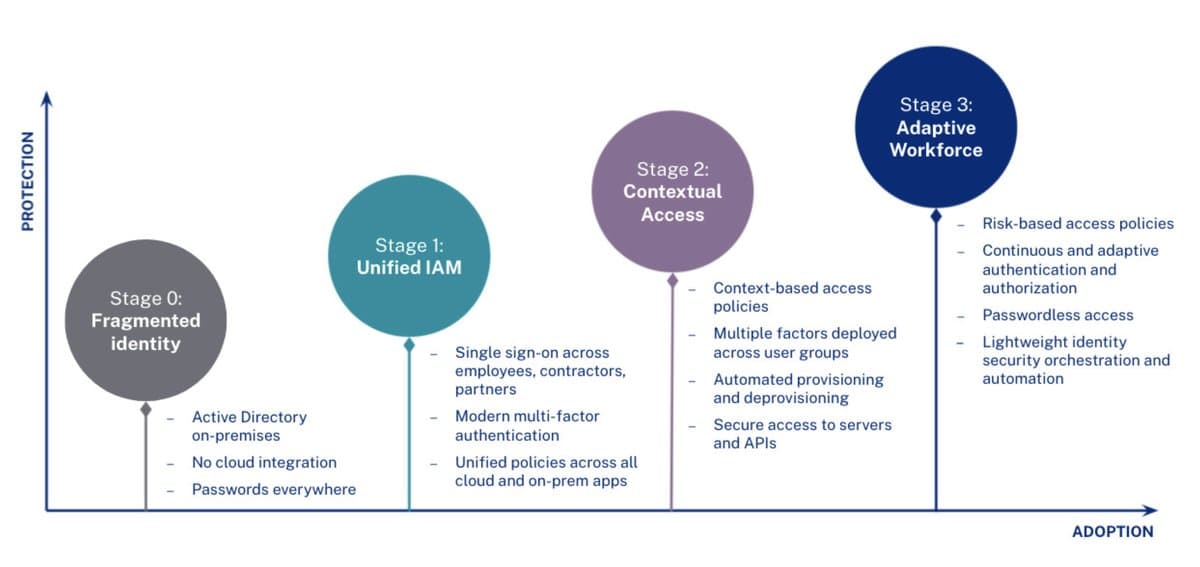
Okta approaches zero trust from the identity angle, building access controls around user authentication and authorization. Their platform has evolved from single sign-on (SSO) to become a full identity governance solution with zero trust principles built throughout.
The platform's strength lies in its ability to integrate with virtually any application or system that supports modern authentication protocols. This makes Okta particularly valuable for organizations with diverse technology stacks that need consistent identity controls across all systems. Organizations using Okta's platform can significantly reduce identity-related security incidents.
Okta's adaptive authentication goes beyond simple multi-factor authentication to include behavioral analysis, device trust, and contextual risk assessment. Users experience smooth access to authorized applications while administrators get detailed visibility into access patterns and potential security risks.
However, Okta's focus on identity means that organizations still need separate solutions for network microsegmentation, endpoint protection, data loss prevention, and threat detection. This can create complexity in managing multiple security platforms and ensuring consistent policy enforcement across all systems.
Check out Okta → provides identity and access management with advanced zero trust authentication capabilities.
Best for Unified Cloud Security: Check Point Zero Trust Platform
Check Point has evolved their traditional network security platform to include zero trust capabilities, creating a solution that spans network monitoring, access controls, threat protection, and policy enforcement. Their approach combines proven network security expertise with modern zero trust principles.
The platform provides enterprise-ready services that address multiple aspects of zero trust security, from network monitoring to advanced threat protection ZDNET. This unified approach appeals to organizations that prefer consolidated platforms over point solutions.
Check Point's threat intelligence integration sets their zero trust platform apart from pure access control solutions. The platform can make dynamic access decisions based on current threat intelligence, automatically adjusting policies when new threats are detected that might affect specific users or applications.
The challenge with Check Point's approach is complexity. Organizations get broad capabilities but may find the platform requires more specialized expertise to deploy and manage effectively compared to simpler point solutions.
Best for DevOps and Infrastructure Access: StrongDM

StrongDM focuses specifically on securing access to databases, servers, infrastructure, and development environments rather than trying to be a full zero trust platform. This specialized approach makes it particularly valuable for DevOps teams and organizations with complex infrastructure environments.
The platform provides granular access controls for infrastructure resources while maintaining detailed audit logs of all administrative activities. Users can access the resources they need without shared credentials or broad administrative privileges, reducing both security risk and compliance complexity.
StrongDM's approach to secrets management goes beyond traditional vault solutions to provide dynamic, just-in-time access credentials. This eliminates the security risks associated with long-lived passwords and API keys while providing the access flexibility that development and operations teams require.
The limitation is scope. StrongDM excels at infrastructure access control but doesn't address other aspects of zero trust security like user device compliance or application-level access controls.
Check out StrongDM → specializes in zero trust access for databases, servers, and infrastructure resources.
Check out StrongDM Managed Secrets → offers advanced secrets management with vault-agnostic, zero trust security controls.
Best for Directory Service Integration: JumpCloud
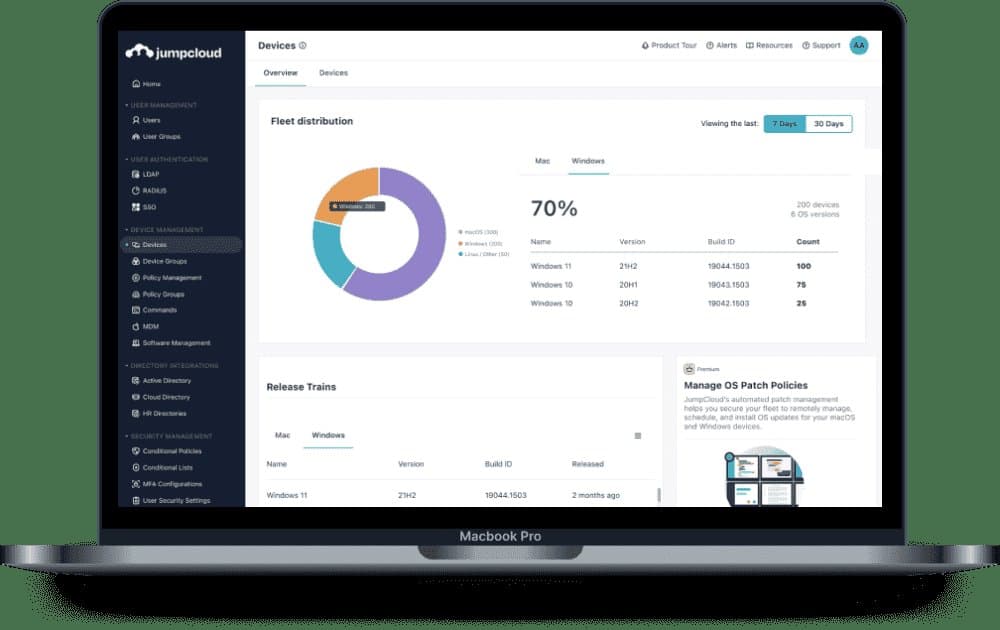
JumpCloud provides a cloud-based directory service that implements zero trust principles for device management and user access control. Their platform is particularly valuable for organizations moving away from traditional on-premises Active Directory while maintaining centralized identity management.
The platform combines device management, user authentication, and application access control in a unified solution that works across Windows, macOS, Linux, and mobile environments. This cross-platform support makes JumpCloud attractive for organizations with diverse endpoint environments that need consistent security policies.
JumpCloud's zero trust implementation focuses on device compliance and user behavior monitoring. Devices that don't meet security requirements are automatically restricted from accessing sensitive resources, while user behavior analysis can detect potential account compromises.
However, JumpCloud's capabilities are primarily focused on endpoint management and basic application access. Organizations with complex network environments or advanced threat protection requirements will likely need additional security platforms to implement full zero trust architecture.
Check out JumpCloud → provides cloud-based directory services with integrated zero trust device and access controls.
Best for Unified Identity Platform: Infisign

Infisign takes a unified approach to identity and access management, combining traditional directory services with modern zero trust access controls. Their platform is designed for organizations that need identity management without the complexity of multiple specialized tools.
The platform provides adaptive authentication, device compliance checking, and application access control through a single management interface. This unified approach reduces administrative overhead while ensuring consistent security policies across all systems and applications.
Infisign's strength lies in its ability to replace multiple identity and access management tools with a single platform. Organizations can consolidate licensing costs while reducing the complexity of managing multiple security systems.
The trade-off is that unified platforms may not provide the specialized capabilities that some organizations need for specific use cases. Organizations with unique requirements may find that specialized tools offer better functionality for their specific needs.
Check out Infisign → offers an identity platform with integrated zero trust access controls and device management.
Best for Browser Security Integration: Seraphic

Seraphic addresses a critical gap in most zero trust implementations: browser-based security. Their platform provides zero trust controls at the browser layer, protecting against web-based attacks that traditional network security might miss.
The platform integrates with existing security tools like CrowdStrike Falcon to provide protection that spans endpoint security and browser-based threats. This integration approach allows organizations to extend their existing security investments rather than replacing them entirely.
Seraphic's browser-layer security is particularly relevant for organizations concerned about AI-driven browsing risks and sophisticated web-based attacks. The platform can enforce zero trust policies at the application layer while users browse the internet or access web-based business applications.
However, browser security represents just one component of zero trust architecture. Organizations will need additional platforms to address network access, device compliance, and other zero trust requirements.
Check out Seraphic → provides browser-layer security with zero trust controls and integration with existing security platforms.
Common Mistakes to Avoid
Trying to Implement Everything at Once
The biggest mistake organizations make is attempting to deploy zero trust architecture in a single project. This approach typically leads to project delays, user resistance, and incomplete implementations that provide limited security value.
Successful zero trust deployments start with specific use cases (remote access, privileged user management, or high-value application protection) and expand gradually. This phased approach allows organizations to learn from early implementations and adjust their strategy based on real-world experience.
Ignoring User Experience During Planning
Zero trust implementations that focus solely on security controls without considering user impact typically fail due to user resistance and workaround behaviors. Users who find security controls frustrating or time-consuming will find ways to bypass them, potentially creating security risks worse than the original problems.
The most successful deployments involve users in the planning process and design security controls that enhance rather than hinder productivity. This might mean accepting slightly less stringent controls in exchange for better user adoption and compliance.
Underestimating Integration Complexity
Many organizations assume that modern zero trust platforms will integrate smoothly with their existing technology infrastructure. In practice, integration challenges often consume more time and resources than the initial platform deployment.
Plan for extensive integration testing, particularly with legacy systems that may not support modern authentication protocols. Budget additional time and resources for custom integration work, especially if your organization has unique or specialized applications.
If You're in a Hurry
For organizations that need to start zero trust implementation immediately, focus on identity and access management first. Platforms like Microsoft Entra (for Microsoft-centric environments) or Okta (for diverse technology stacks) provide the foundation for zero trust architecture while delivering immediate security value.
Add network access controls and device compliance capabilities in subsequent phases once the identity foundation is solid.
Vivian Cross covers enterprise security tools and zero trust architecture for organizations serious about measurable protection. Her analysis focuses on production deployment data and real-world security outcomes rather than vendor marketing claims.
Get our best picks delivered weekly
Reviews, deals, and guides. No spam.